In software development, it’s inevitable that you’ll want to outsource some work, especially as you grow. You might need a pesky plugin altered, or you need help with enterprise-level software integration.
Eventually, you’ll need to grant password access to an off-site contractor. But how do you do it securely?
Let me tell you a quick story about an agency I’d contracted to help with the deployment of an application. This was a significant project, and we had contractors with us from the start. One morning, I logged into my computer to find an email from one of the contractors that included an image. The image was a screen capture of a server address and an admin-level username & password. These days, I hope it’s universally understood that there are three things you never send in an unencrypted email:
- Credit card information.
- Social security numbers.
- Passwords.
I immediately called him on the phone. He was mortified about what had happened. But what concerned me the most was what he had said during the conversation. “I just forwarded it along as it was from my team member.” Which meant it had circulated around his office before I’d ever gotten it.
💌 Get more tips like these in your inbox! Sign up for our biweekly newsletter today and join 15,000+ other fellow marketers who count on our content.
Implications of a password incident
The information security industry follows key criteria to assess the severity of security incidents, including:
- Was there an actual security breach because of the leaked credentials?
- Who has possession of the information?
Understanding this helps determine the best course of action to contain and remediate the incident. In my case, our two companies contained information between us. We were fortunate. The potential business implications of a significant security breach are nightmares. Had there been a legitimate breach, it would have exposed sensitive client and employee data. It would have revealed financial information. It could have led to theft of social security numbers. And, depending on your industry, this could have made the local or national news.
You might also like: Email Marketing Basics
Remediating a security incident
Your first step will always be to put together your IT team. The sooner you can communicate the issue, the better your outcome will be. Too often, people will (understandably) be reactionary. Take a moment to recount where you stand, and make sure all the key players are at the table. Then, you can put together an effective plan to move forward. This would generally include:
- Block access to the compromised system, change passwords, and begin an audit of the server logs.
- Notify the contractor. If they have a security team, have them work with your IT department to effect any needed changes. If they are at fault, they will probably not charge you for this work.
- Clean up the trail. Mail doesn’t just live in your inbox. The message lives on email servers in your environment and the contractor’s. Make sure to delete the email from all email clients and servers on both sides.
- Develop a plan with the contractor for future communications that involve passwords.
- If you’re not comfortable having the person who sent the email on the project, ask to have them replaced. This may cause delays in the timeline, but it’s worth it. You have to be comfortable with the people who have access to your most sensitive business data.
Preventing credentials leakage can prove to be less expensive than treating a security incident. If you are using a mobile device management tool, make sure to disable the screen capture option on the users’ BYOD (Bring Your Own Device) or COPE (Corporate-Owned, Personally Enabled) devices.
How to send passwords securely
Advance planning could have prevented this incident. It’s important to lay out the ground rules before the job starts. When it comes to the secure communication of passwords, you have a few options.
1. Communicate passwords verbally
One of the safest ways to share passwords is verbally, either in person or over the phone. This ensures that sensitive credentials are never stored in emails, chat logs, or written documents that could be intercepted.
However, always confirm you’re speaking to the intended recipient before sharing any details and that the call is not recorded. If you’re meeting in person, avoid writing the password down on paper or typing it into a device where prying eyes or screen-recording software could capture it.
While this method is highly secure, it’s not always practical—especially if you work with remote contractors across different time zones. In such cases, it’s best used for one-time passwords or temporary access, combined with a follow-up policy for resetting credentials after use.
2. Send passwords via encrypted emails
Another way to securely share passwords is through encrypted emails. Unlike standard emails, which can be intercepted during transmission, encrypted emails ensure that only the intended recipient can access the information.
Sending passwords via unencrypted emails is never recommended, as emails are often stored in multiple locations—on email servers, in backups, and in recipients’ inboxes—where they could be accessed by hackers, IT staff, or even unauthorized employees.
To securely share passwords via email, you’ll need to use end-to-end encryption. This method scrambles the email’s contents so that only the recipient with the correct decryption key can read it. While setting up encrypted email may require some initial configuration, it provides a long-term security benefit, especially when working with external contractors or team members who require ongoing access to sensitive information.
There are several open-source tools available for encrypting emails. One widely used option is Enigmail, a PGP (Pretty Good Privacy) encryption tool that integrates with Thunderbird, allowing you to send and receive encrypted messages effortlessly.

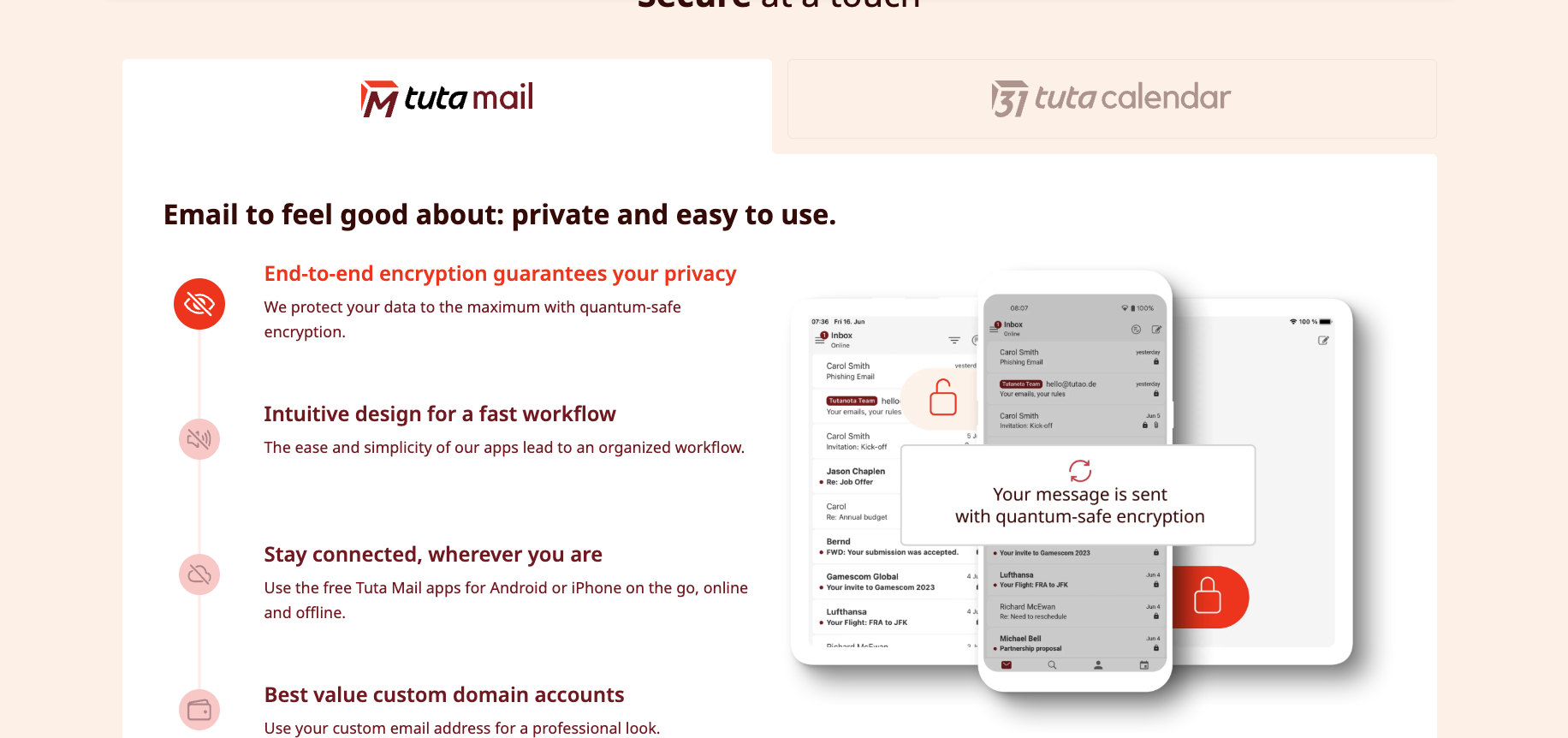
Other alternatives include ProtonMail, which offers built-in encryption with no setup required, and Tutanota, a privacy-focused email service with automatic encryption.
If you use Gmail or Outlook, you can enhance security with tools like FlowCrypt or Virtru, which provide encryption layers on top of existing email services.

Best Practices for Secure Email Encryption:
- Always confirm the recipient’s identity before sharing passwords.
- Never store decrypted passwords in your email inbox—once the recipient has accessed them, delete the email from all mail servers.
- Use passphrase-protected emails whenever possible, ensuring that only someone with the correct passphrase can decrypt the message.
- Set expiration dates for encrypted emails so that passwords are no longer accessible after a set period.
While encrypting emails requires a slight learning curve, it’s an excellent solution for maintaining long-term secure communication channels between teams, contractors, and business partners. If you frequently share passwords via email, it’s worth investing time in setting up a simple encryption workflow to protect your sensitive credentials.
3. Use a password vault
Another highly secure way to share passwords is to store them in a password vault file, such as KeePass, and then share access through a secure channel.
What is a password vault?
A password vault is an encrypted file or cloud-based storage system that contains usernames, passwords, addresses, API keys, and other sensitive credentials. These vaults encrypt stored data using industry-standard encryption (AES-256, ChaCha20) and require a master password or biometric authentication to access.
Why Use a Password Vault?
Password vaults protect credentials from unauthorized access, phishing attacks, and accidental leaks. They are especially useful for teams managing multiple accounts or working with external contractors.
One key advantage of using a password vault is Role-Based Access Control (RBAC). Cloud-based solutions like 1Password and LastPass allow administrators to set specific permissions for each team member. This means that not everyone gets full access to all credentials, ensuring that sensitive passwords are only accessible to those who truly need them.

Another major benefit is audit logs and activity tracking, which enhance visibility and accountability. Tools like Bitwarden provide detailed logs that let administrators monitor when passwords are accessed, who accessed them, and from where.

This feature is useful for organizations that need to comply with security regulations or manage large teams with multiple access points. If a security breach or misuse occurs, administrators can instantly revoke access, minimizing potential damage.
For temporary access needs, some password managers offer one-time access links. Platforms like Dashlane allow you to generate login links that expire after a single use, ensuring that credentials aren’t left exposed indefinitely. This feature is particularly useful when working with short-term contractors or external vendors who only need temporary access to specific accounts.

Finally, automatic password expiry is another essential feature found in many password managers. Instead of relying on manual password updates, these tools can be configured to rotate passwords after a set period automatically. This reduces the risk of old credentials being reused or remaining active long after an employee has left the company. Regular password rotation helps maintain strong security hygiene and prevents unauthorized access over time.
Best Practices for Password Vaults
- Use a strong master password for the vault (at least 16+ characters with uppercase, lowercase, numbers, and symbols).
- Enable Two-Factor Authentication (2FA) for an extra security layer.
- Set up auto-lock and time-based expiry to prevent unauthorized access.
- Regularly update stored passwords and use unique passwords for each service.
By using password managers and vaults, you can eliminate risky password-sharing practices, grant temporary or restricted access, and prevent unauthorized use of credentials.
A password vault combined with secure communication methods significantly enhances security, compliance, and overall password hygiene.
To make this effective all around, you’ll want to start with a strong foundation. When you start talking to potential contractors, ask them how they handle password storage and communication. Build those restrictions into your contract. Create strong passwords from the start. The 16-character combination of upper and lower case letters, numbers, and symbols will be your most secure.
Read more on the blog:
1. Mailchimp vs. GetResponse: in-depth comparison
Moving Toward a Passwordless Future
As cybersecurity evolves, businesses are increasingly adopting passwordless authentication methods to eliminate the need for password sharing altogether.
Biometric authentication, such as fingerprint or facial recognition, is becoming more widely used. Passkeys and WebAuthn technologies, like those offered by Apple and Google, are also gaining popularity as secure alternatives to traditional passwords.
Hardware security keys, such as YubiKey or SoloKeys, offer an additional layer of protection, ensuring that only authorized users can access sensitive accounts. Meanwhile, one-time authentication links, also known as magic links, allow users to log in without entering a password. These innovations significantly reduce the risk of credential theft and simplify secure access management.

Single Sign-On (SSO), for example, allows users to access multiple accounts with a single login. Services like Google Workspace, Microsoft Entra ID, and Okta ensure that employees and contractors don’t need direct access to credentials while maintaining security.

For businesses managing complex systems, access management tools such as AWS IAM Roles, Cloudflare Access, and JumpCloud enable organizations to assign role-based permissions instead of sharing static passwords.
Additionally, OAuth authentication and API keys offer another secure way to grant third-party access without disclosing login details. These approaches drastically lower the chances of a security breach while maintaining the necessary level of access for contractors.
Ready? Set… secure!
Are you confident about how your business handles its passwords? With advanced planning, you can prevent huge headaches and foster a good business relationship. If you have an IT Team, ask them how you currently store and communicate passwords. If they don’t have a policy in place, that’s okay. But, make sure it’s something they develop before you hire outside contractors. Do you have any questions? Have you used other sharing strategies or password vault apps? Share them below!
Learn more: Online security 101 for SMBs
